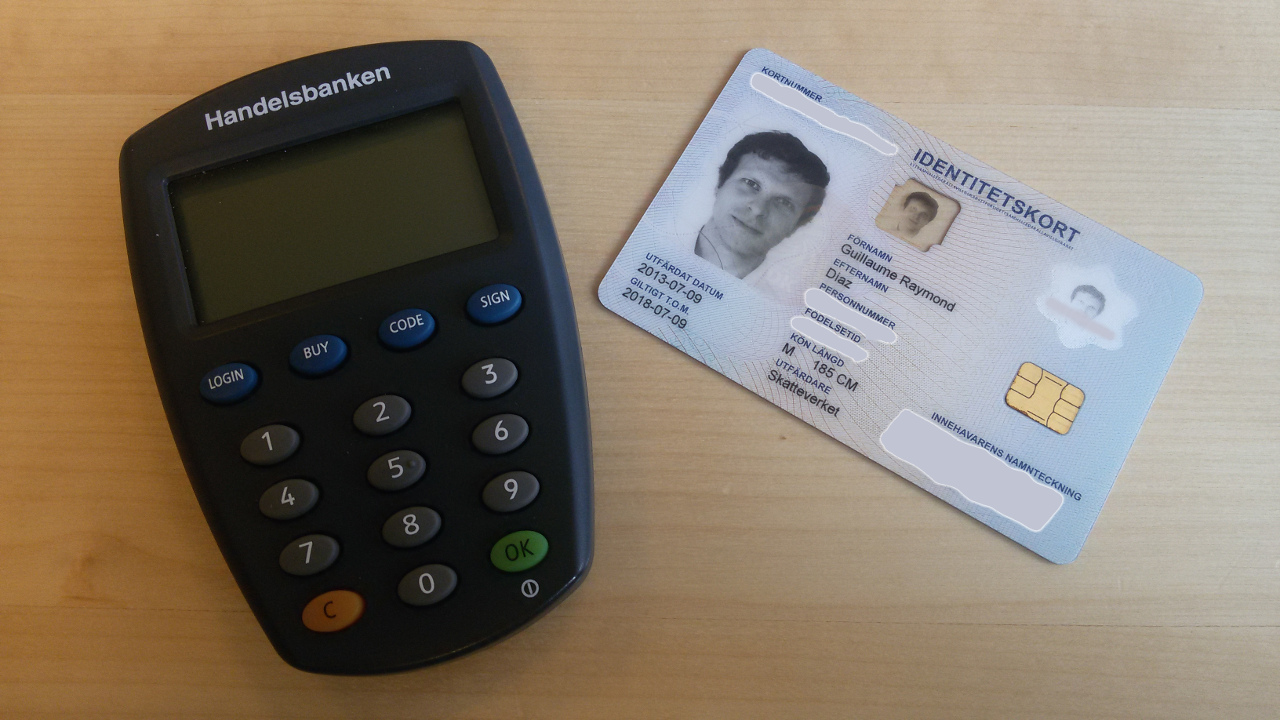
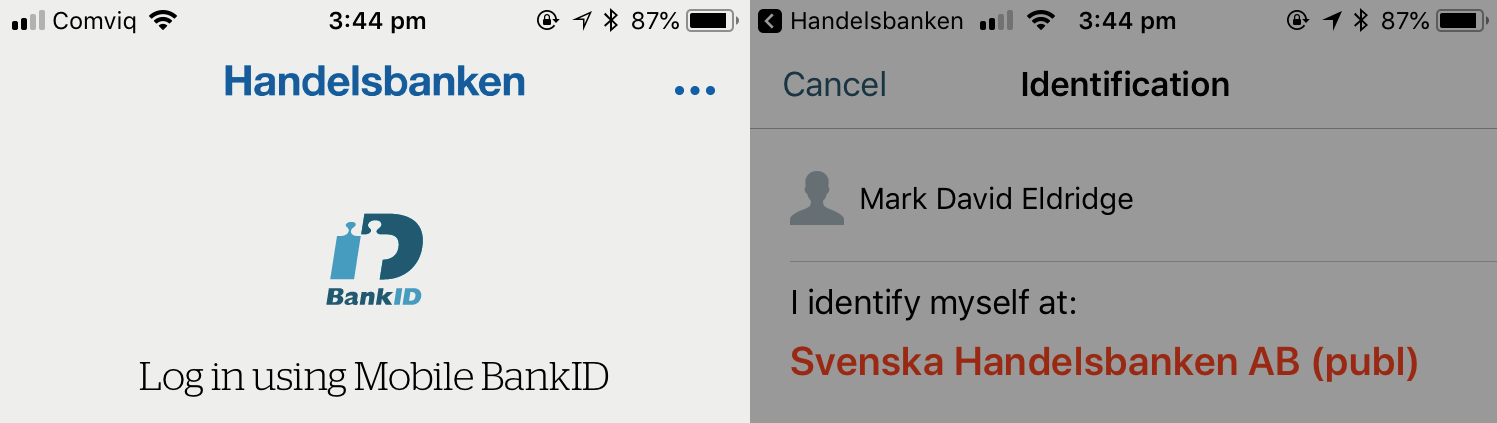
One of the less fun aspects of moving countries is that you're a walking edge-case for many IT systems. Being an expat also means becoming intimately familiar with all of the differences in how government services verify the identity of their users.
We need to take two things much more seriously: the security of our supply-chain, and the security of our baseboard management controllers.
Having 50 million accounts breached is bad enough, but the bigger issue is that a huge number of third-party services use Facebook to authenticate their users.
In a modern DevOps environment, development teams manage the security of their own systems. In an environment where deployments happen several times a day, this model scales far better than the historical practice of security acting as a gatekeeper to production.
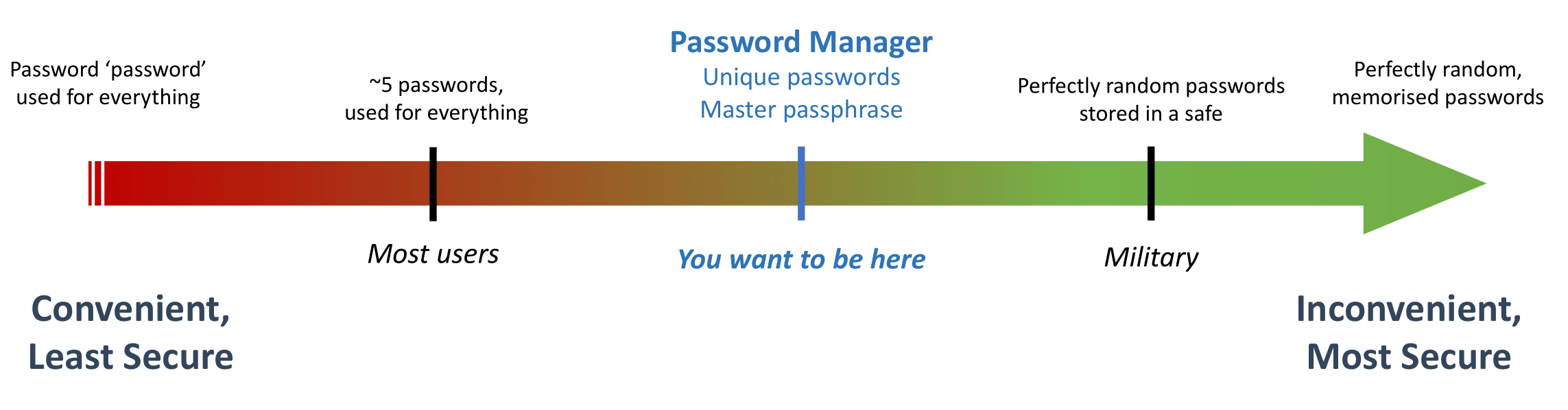
Everything we do in the security industry is a trade-off between convenience and security. The important thing is to be honest about the compromises you are making, and why they are necessary.
In my last email I mentioned Alex Stamos' Twitter takedown of the 'Digi-ID' authentication solution. Buried in the exchange was a mention by Stamos of the Web Authentication standard, which is something you'll be hearing a lot more about in coming months.